最右APP协议加密算法分析笔记
IDA7.0
lldb
Charles
本次分析的版本是4.2.1(在目前最新版本4.6.4中依然适用)
开始前先进行如下步骤
1.app砸壳后用IDA加载
2.配置抓包工具charles
ok 开始前不会使用Charles的可以搜索关键字"Charles ios https"或直接查看该链接"https://www.xzb.cc/tutorial/4365.html" 其中https如何抓包都有详细讲解 此处不在赘述
首先开启抓包工具 打开APP刷新内容抓包结果如下
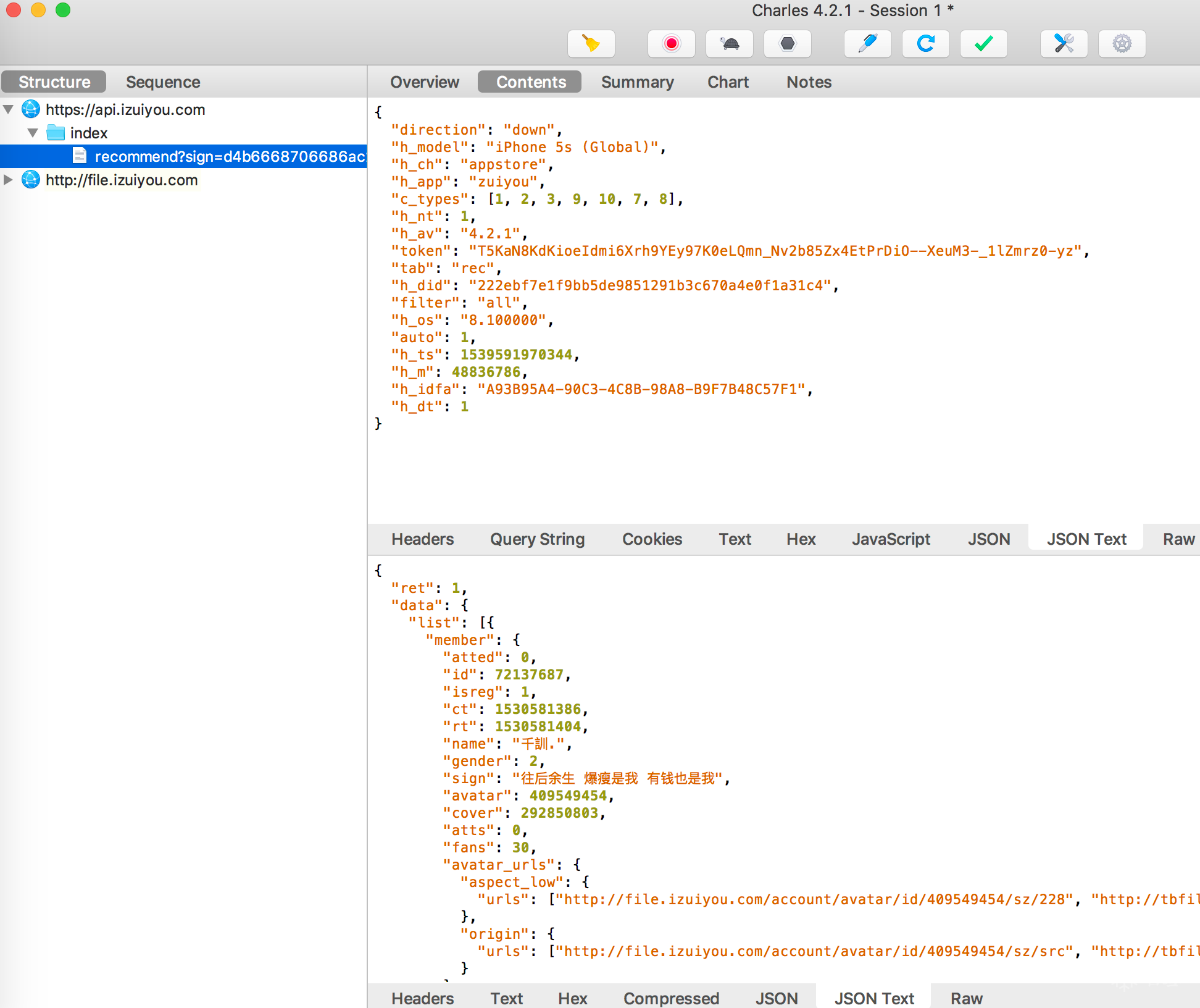
通过POST请求可以看到url上有个"sign"参数,每次请求该sign都会发生变化,接下来使用IDA进行分析该参数来源。
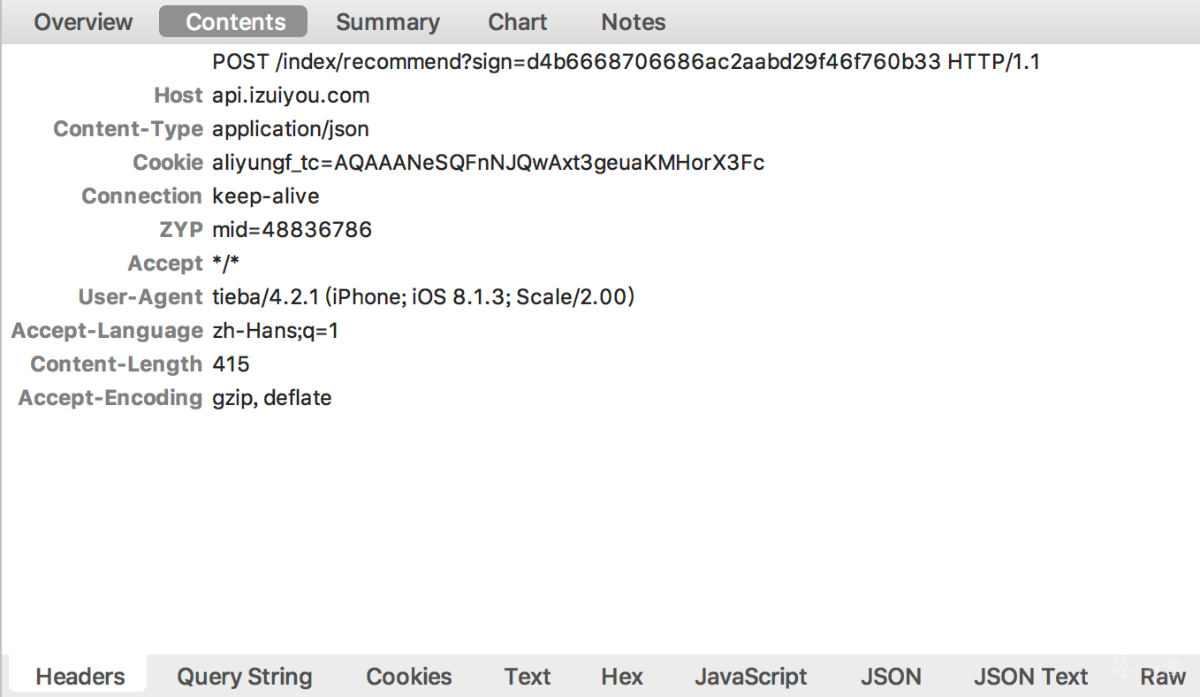
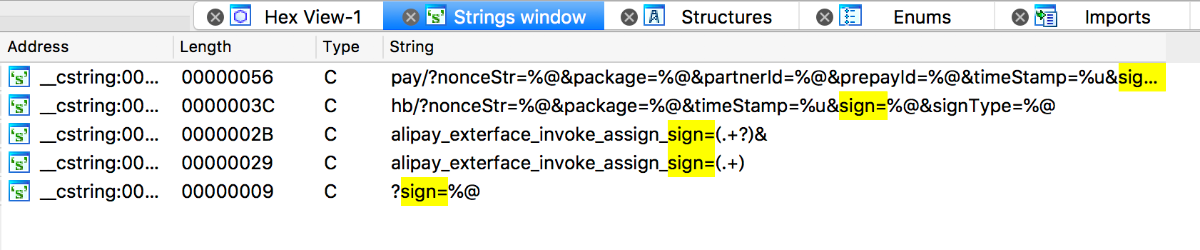
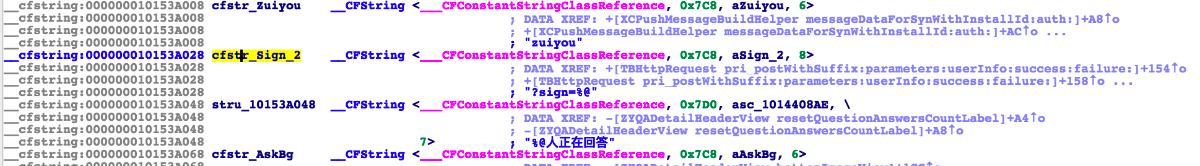
IDA中字符串搜索"sign=" 根据字符串推测是最后一个 鼠标左键双击进入
看到下图
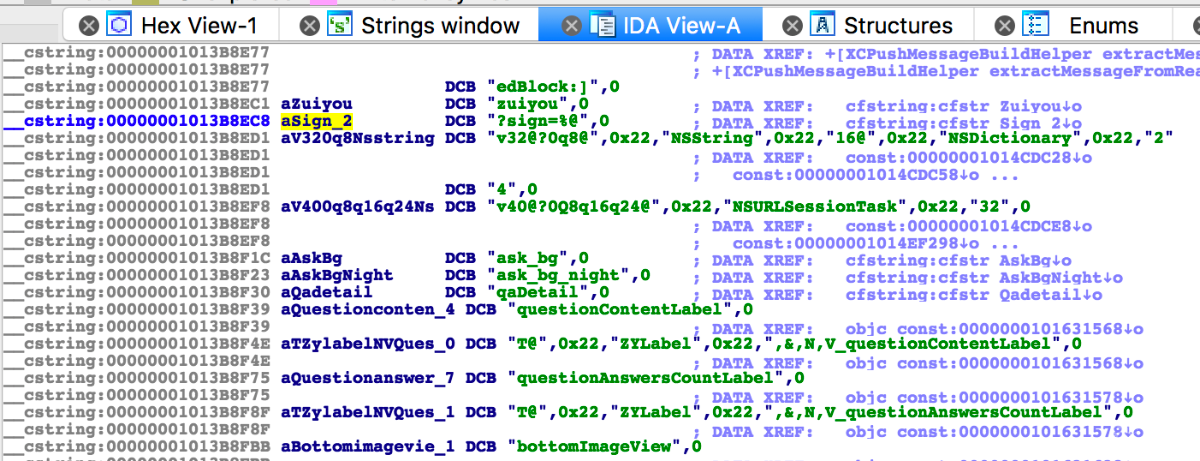
在图中高亮处按下X键或者右键选中“jump to xref to operand”
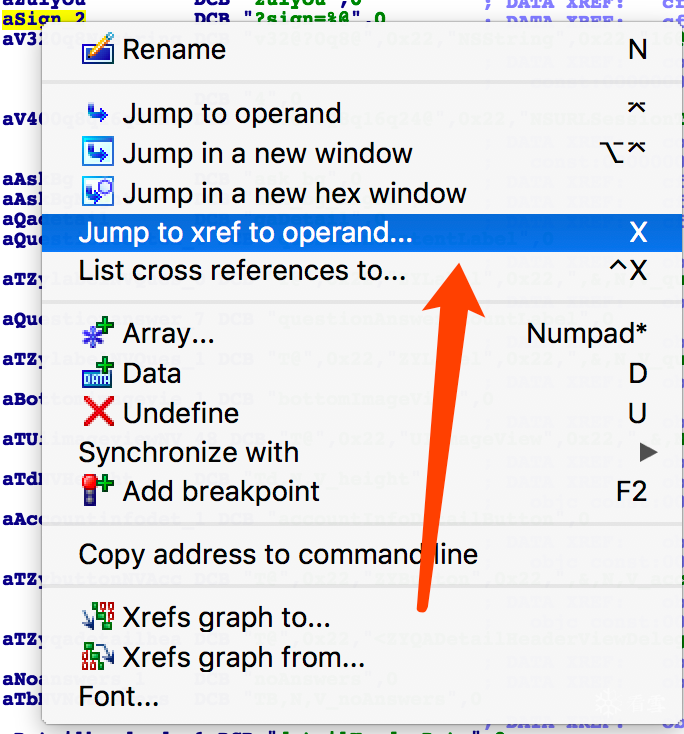
弹出如下内容 点击ok
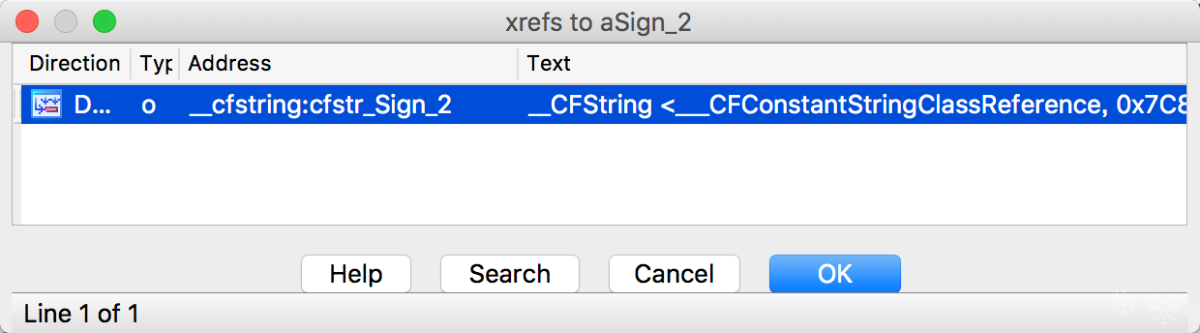
继续在图中高亮处按下X键或者右键选中“jump to xref to operand”
弹出如下内容
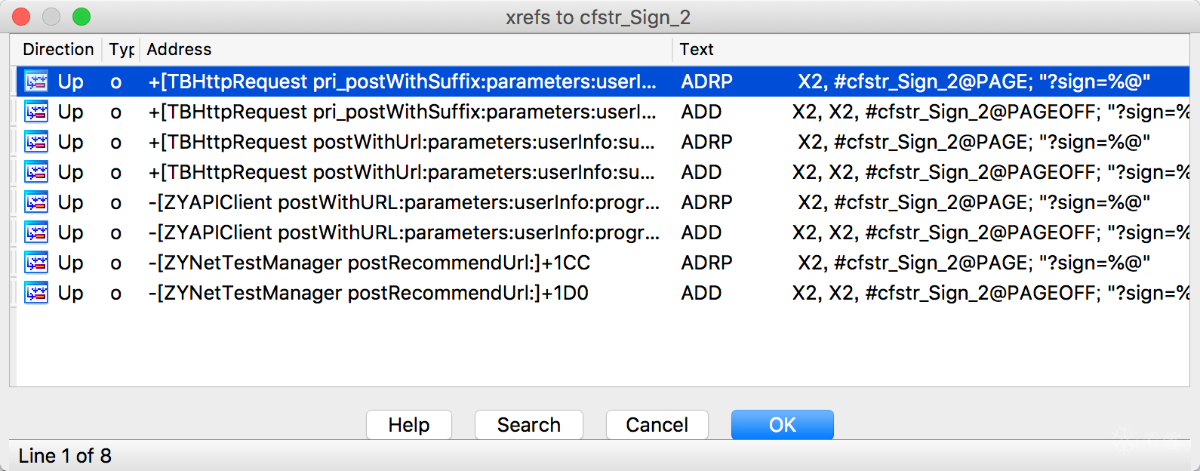
根据分析得知"[ZYAPIClient postWithURL:parameters]"中有sign来源 双击进入
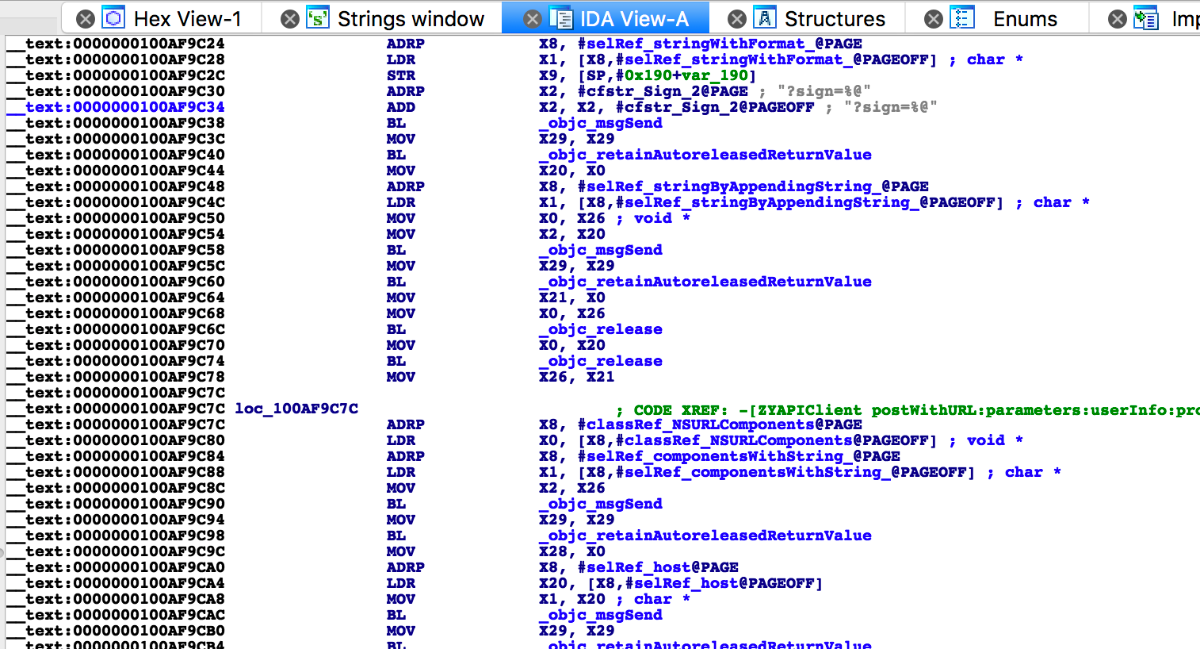
按下f5转换为伪代码进行查看
如上图所示 sign的参数是通过调用"ZYAPIClient signWithParameters"返回的
此时先不关注v27参数内容是什么 等下动态调试再来看该参数内容
通过代码知道调用"ZYAPIClient signWithParameters"后返回sign值
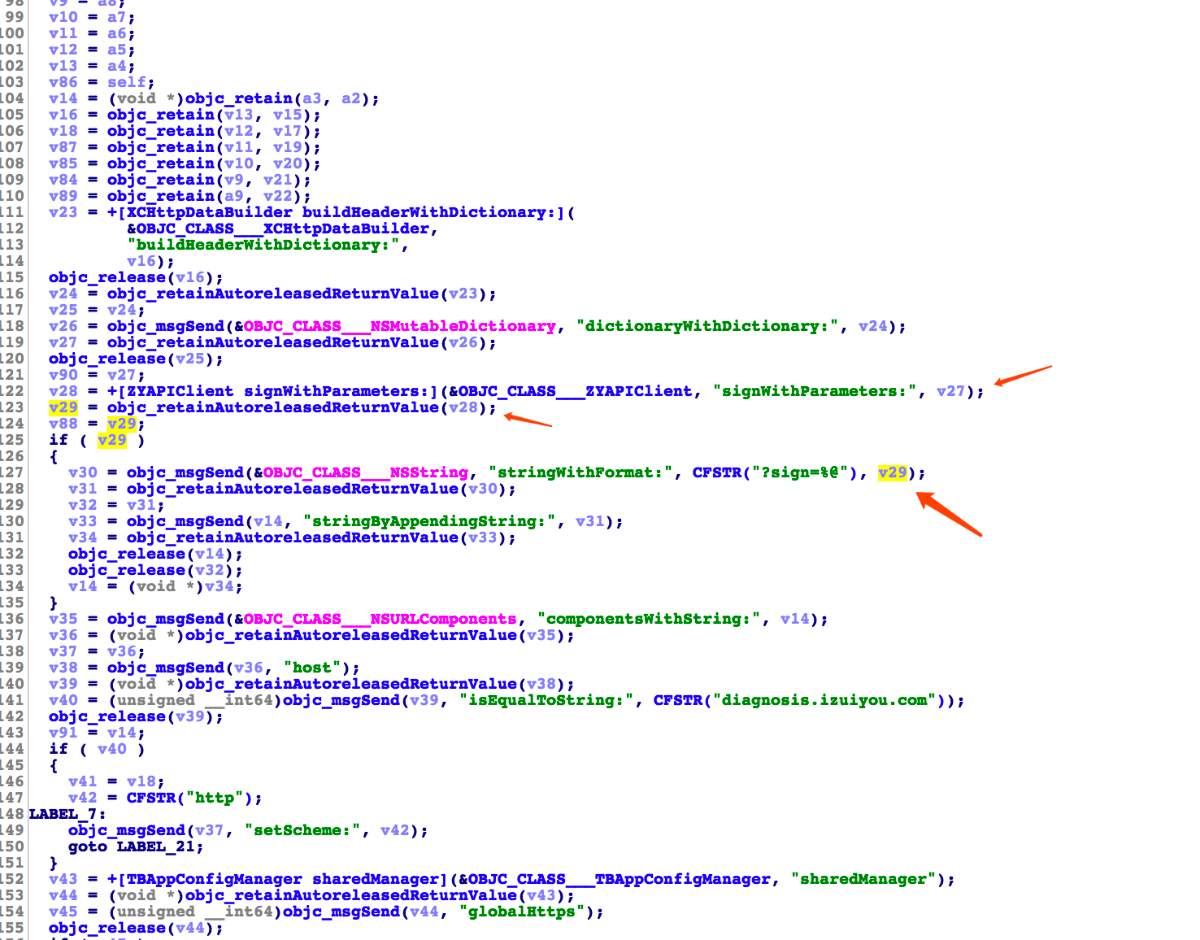
继续使用IDA进行分析 在函数窗口中搜索“ZYAPIClient signWithParameters”双击跳转到如下图
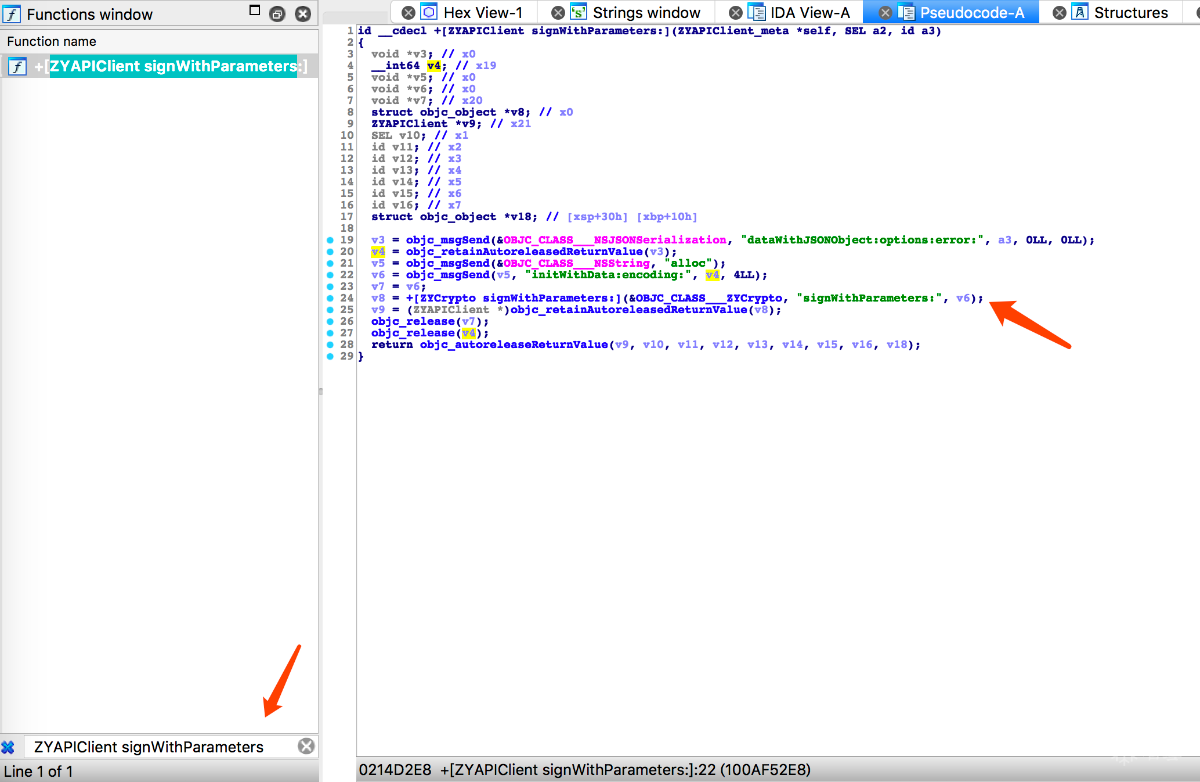
得知参数是由“ZYCrypto signWithParameters”返回 那么函数窗口中继续搜索“ZYCrypto signWithParameters”
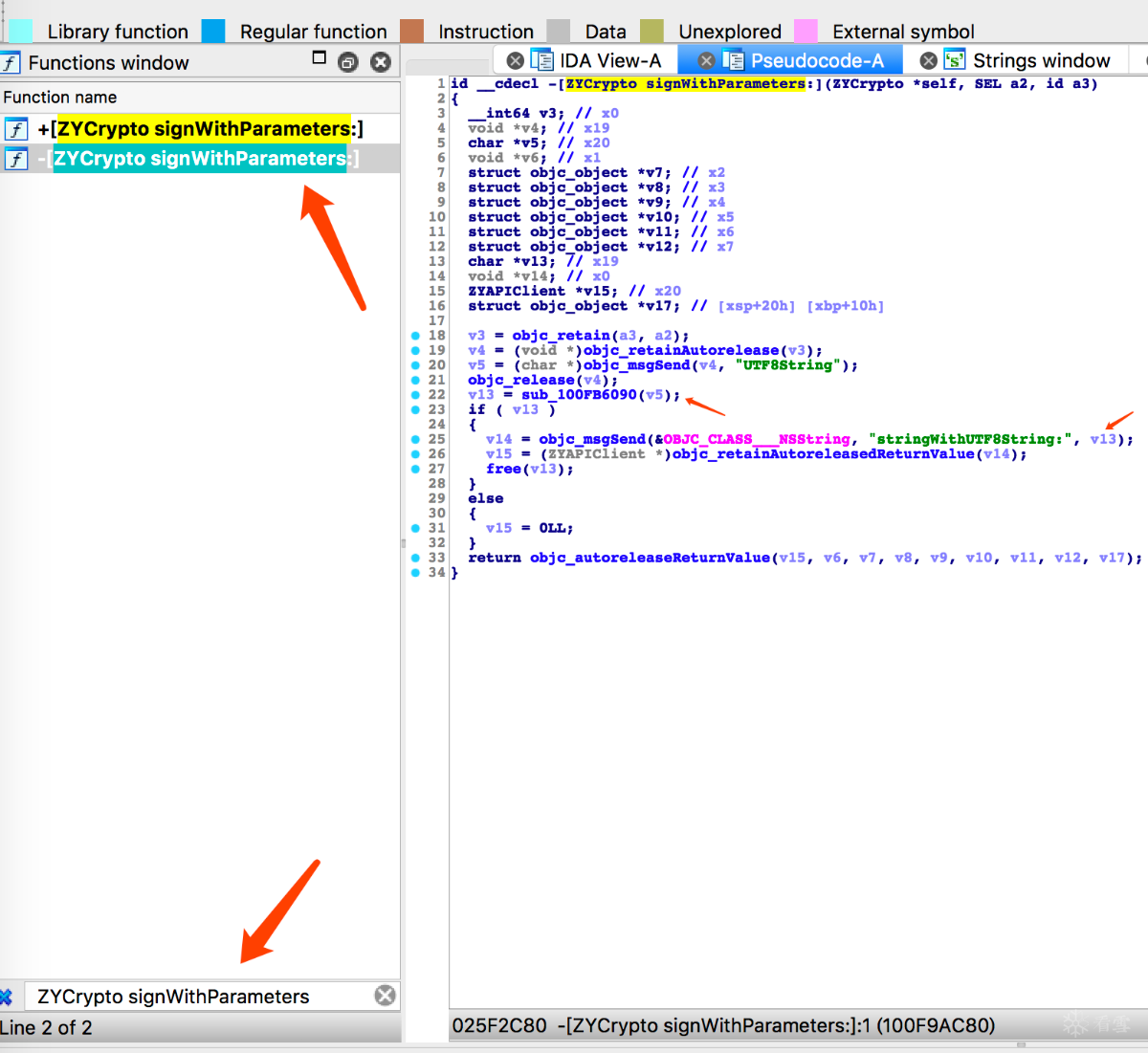
得知数据是调用了“sub_100FB6090”函数返回的 双击函数进入查看伪代码
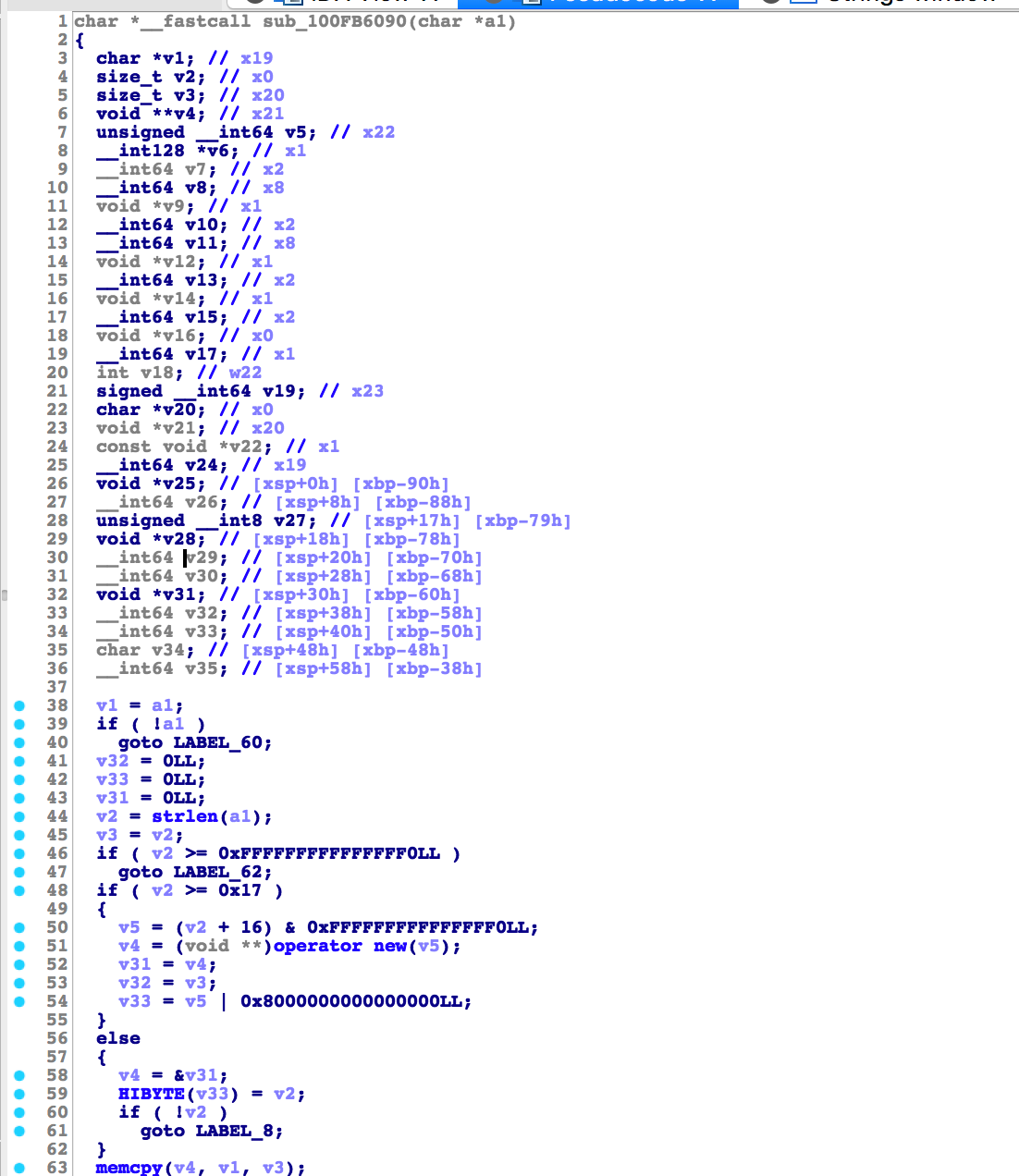
查看代码得知还调用了"sub_100DB274C"和"sub_100FB6004"两个函数 接下来查看这两个函数
跳转到“sub_100DB274C”函数后肉眼可以看出是一系列循环位操作计算 流程图如下 逻辑清晰 无混淆 看起来并不复杂 代码量不算多
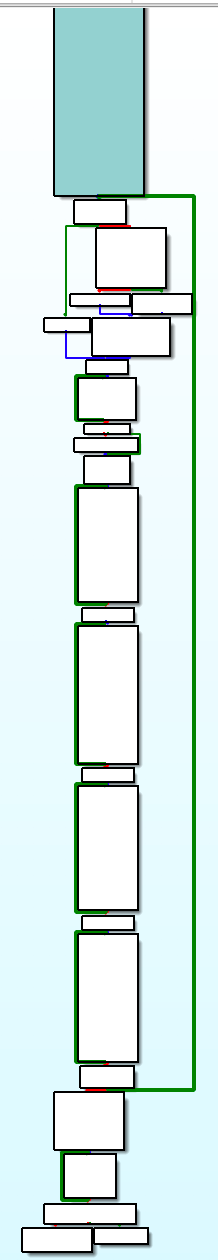
函数“sub_100FB6004”如下图
函数到此为止 记录下调用流程
"ZYAPIClient signWithParameters" -> "ZYCrypto signWithParameters" -> "sub_100FB6090" -> "sub_100DB274C" -> "sub_100FB6004"
接下来就是动态调试拿到调用函数时传入的参数及还原成c代码即可 下面开始动态调试(对于lldb的配置此处不再赘述)
首先ssh到手机
ssh root@ip
打开最右app 然后在ssh查找app进程
ps -e |grep var
//////////////////////////////////////////////////////////////////////////
iphone5s:~ root# ps -e |grep var
372 ?? 0:00.06 /usr/libexec/pkd -d/var/db/PlugInKit-Annotations
632 ?? 0:01.69 /var/mobile/Containers/Bundle/Application/84BED02F-A270-4B92-868D-3C4A6F564F28/tieba.app/tieba
641 ttys000 0:00.01 grep var
debugserver附加
debugserver *:1234 --attach=pid
//////////////////////////////////////////////////////////////////////////
iphone5s:~ root# debugserver *:1234 --attach=632
debugserver-@(#)PROGRAM:debugserver PROJECT:debugserver-320.2.89
for arm64.
Attaching to process 632...
Listening to port 1234 for a connection from *...
打开lldb连接到越狱后的手机(可能卡住一段时间 耐心等待)
YoudeMacBook-Pro:~ youfuck$ lldb
(lldb) process connect connect://172.16.4.29:1234
Process 632 stopped
* thread #1, queue = 'com.apple.main-thread', stop reason = signal SIGSTOP
frame #0: 0x0000000194f24e7c libsystem_kernel.dylib`mach_msg_trap + 8
libsystem_kernel.dylib`mach_msg_trap:
-> 0x194f24e7c <+8>: ret
libsystem_kernel.dylib`mach_msg_overwrite_trap:
0x194f24e80 <+0>: mov x16, #-0x20
0x194f24e84 <+4>: svc #0x80
0x194f24e88 <+8>: ret
Target 0: (tieba) stopped.
以上lldb已经附加到app 接下来对之前找到的关键位置下断点进行调试
先获取模块基地址
image list -o -f 模块名称
//////////////////////////////////////////////////////////////////////////
(lldb) image list -o -f tieba
[ 0] 0x000000000004c000 /private/var/mobile/Containers/Bundle/Application/84BED02F-A270-4B92-868D-3C4A6F564F28/tieba.app/tieba(0x000000010004c000)
此时lldb调试先看调用"sub_100FB6090"时传入的参数(为什么不从之前的函数下断 因为之前的函数通过伪代码可以看出并没什么修改数据 所以直接在此处下断点)
下断点 "br s -a 模块基地址+ida中看到的函数地址" 然后在app中刷新一下即可触发断点
(lldb) br s -a 0x4c000+0x100FB6090
Breakpoint 2: where = tieba`Assimp::FBX::Connection::Compare(Assimp::FBX::Connection const*) const + 10732152, address = 0x0000000101002090
断下后查看参数 查看参数1即x0 可以看出字符串就是抓包时所发送的数据
(lldb) x $x0 $x0+600
0x157575c38: 7b 22 64 69 72 65 63 74 69 6f 6e 22 3a 22 64 6f {"direction":"do
0x157575c48: 77 6e 22 2c 22 68 5f 6d 6f 64 65 6c 22 3a 22 69 wn","h_model":"i
0x157575c58: 50 68 6f 6e 65 20 35 73 20 28 47 6c 6f 62 61 6c Phone 5s (Global
0x157575c68: 29 22 2c 22 68 5f 63 68 22 3a 22 61 70 70 73 74 )","h_ch":"appst
0x157575c78: 6f 72 65 22 2c 22 68 5f 61 70 70 22 3a 22 7a 75 ore","h_app":"zu
0x157575c88: 69 79 6f 75 22 2c 22 63 5f 74 79 70 65 73 22 3a iyou","c_types":
0x157575c98: 5b 31 2c 32 2c 33 2c 39 2c 31 30 2c 37 2c 38 5d [1,2,3,9,10,7,8]
0x157575ca8: 2c 22 68 5f 6e 74 22 3a 31 2c 22 68 5f 61 76 22 ,"h_nt":1,"h_av"
0x157575cb8: 3a 22 34 2e 32 2e 31 22 2c 22 74 6f 6b 65 6e 22 :"4.2.1","token"
0x157575cc8: 3a 22 54 35 4b 61 4e 38 4b 64 4b 69 6f 65 49 64 :"T5KaN8KdKioeId
0x157575cd8: 6d 69 36 58 72 68 39 59 45 79 39 37 4b 30 65 4c mi6Xrh9YEy97K0eL
0x157575ce8: 51 6d 6e 5f 4e 76 32 62 38 35 5a 78 34 45 74 50 Qmn_Nv2b85Zx4EtP
0x157575cf8: 72 44 69 4f 2d 2d 58 65 75 4d 33 2d 5f 31 6c 5a rDiO--XeuM3-_1lZ
0x157575d08: 6d 72 7a 30 2d 79 7a 22 2c 22 74 61 62 22 3a 22 mrz0-yz","tab":"
0x157575d18: 72 65 63 22 2c 22 68 5f 64 69 64 22 3a 22 32 32 rec","h_did":"22
0x157575d28: 32 65 62 66 37 65 31 66 39 62 62 35 64 65 39 38 2ebf7e1f9bb5de98
0x157575d38: 35 31 32 39 31 62 33 63 36 37 30 61 34 65 30 66 51291b3c670a4e0f
0x157575d48: 31 61 33 31 63 34 22 2c 22 66 69 6c 74 65 72 22 1a31c4","filter"
0x157575d58: 3a 22 61 6c 6c 22 2c 22 68 5f 6f 73 22 3a 22 38 :"all","h_os":"8
0x157575d68: 2e 31 30 30 30 30 30 22 2c 22 61 75 74 6f 22 3a .100000","auto":
0x157575d78: 31 2c 22 68 5f 74 73 22 3a 31 35 33 39 37 34 37 1,"h_ts":1539747
0x157575d88: 30 39 35 37 31 32 2c 22 68 5f 6d 22 3a 34 38 38 095712,"h_m":488
0x157575d98: 33 36 37 38 36 2c 22 68 5f 69 64 66 61 22 3a 22 36786,"h_idfa":"
0x157575da8: 41 39 33 42 39 35 41 34 2d 39 30 43 33 2d 34 43 A93B95A4-90C3-4C
0x157575db8: 38 42 2d 39 38 41 38 2d 42 39 46 37 42 34 38 43 8B-98A8-B9F7B48C
0x157575dc8: 35 37 46 31 22 2c 22 68 5f 64 74 22 3a 31 7d 00 57F1","h_dt":1}.
0x157575dd8: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 f0 ...............�
0x157575de8: 00 00 00 00 00 00 00 f0 11 00 00 00 00 00 00 00 .......�........
0x157575df8: 13 15 00 00 c0 00 00 00 03 64 00 00 23 a9 00 00 ....�....d..#�..
0x157575e08: 00 00 00 00 00 00 00 10 21 43 50 58 05 00 00 00 ........!CPX....
0x157575e18: 00 f0 00 00 98 00 00 00 02 00 00 00 71 75 65 72 .�..........quer
0x157575e28: 79 00 00 00 00 80 00 00 6c 00 00 00 31 6a 30 0b y.......l...1j0.
0x157575e38: 0c 06 72 5f 44 61 74 61 01 01 01 30 0c 0c 04 73 ..r_Data...0...s
0x157575e48: 79 6e 63 0c 04 73 79 6e 61 30 0d 0c 05 63 6c 61 ync..syna0...cla
0x157575e58: 73 73 0c 04 67 65 6e 70 30 12 0c 04 61 63 63 74 ss..genp0...acct
0x157575e68: 0c 0a 69 64 66 61 41 63 6f 75 6e 74 30 13 0c 04 ..idfaAcount0...
0x157575e78: 73 76 63 65 0c 0b 69 64 66 61 53 65 72 76 69 63 svce..idfaServic
0x157575e88: 65 30 15 0c 07 6d 5f 4c e0...m_L
对“sub_100DB274C”下断点
br s -a 0x4c000+0x100DB274C
调用"sub_100DB274C"时参数如下
(lldb) x $x0 $x0+0x1ab
0x1576d0670: 59 30 4d 54 42 6c 4f 44 63 78 6e 22 3a 22 64 6f Y0MTBlODcxn":"do
0x1576d0680: 77 6e 22 2c 22 68 5f 6d 6f 64 65 6c 22 3a 22 69 wn","h_model":"i
0x1576d0690: 50 68 6f 6e 65 20 35 73 20 28 47 6c 6f 62 61 6c Phone 5s (Global
0x1576d06a0: 29 22 2c 22 68 5f 63 68 22 3a 22 61 70 70 73 74 )","h_ch":"appst
0x1576d06b0: 6f 72 65 22 2c 22 68 5f 61 70 70 22 3a 22 7a 75 ore","h_app":"zu
0x1576d06c0: 69 79 6f 75 22 2c 22 63 5f 74 79 70 65 73 22 3a iyou","c_types":
0x1576d06d0: 5b 31 2c 32 2c 33 2c 39 2c 31 30 2c 37 2c 38 5d [1,2,3,9,10,7,8]
0x1576d06e0: 2c 22 68 5f 6e 74 22 3a 31 2c 22 68 5f 61 76 22 ,"h_nt":1,"h_av"
0x1576d06f0: 3a 22 34 2e 32 2e 31 22 2c 22 74 6f 6b 65 6e 22 :"4.2.1","token"
0x1576d0700: 3a 22 54 35 4b 61 4e 38 4b 64 4b 69 6f 65 49 64 :"T5KaN8KdKioeId
0x1576d0710: 6d 69 36 58 72 68 39 59 45 79 39 37 4b 30 65 4c mi6Xrh9YEy97K0eL
0x1576d0720: 51 6d 6e 5f 4e 76 32 62 38 35 5a 78 34 45 74 50 Qmn_Nv2b85Zx4EtP
0x1576d0730: 72 44 69 4f 2d 2d 58 65 75 4d 33 2d 5f 31 6c 5a rDiO--XeuM3-_1lZ
0x1576d0740: 6d 72 7a 30 2d 79 7a 22 2c 22 74 61 62 22 3a 22 mrz0-yz","tab":"
0x1576d0750: 72 65 63 22 2c 22 68 5f 64 69 64 22 3a 22 32 32 rec","h_did":"22
0x1576d0760: 32 65 62 66 37 65 31 66 39 62 62 35 64 65 39 38 2ebf7e1f9bb5de98
0x1576d0770: 35 31 32 39 31 62 33 63 36 37 30 61 34 65 30 66 51291b3c670a4e0f
0x1576d0780: 31 61 33 31 63 34 22 2c 22 66 69 6c 74 65 72 22 1a31c4","filter"
0x1576d0790: 3a 22 61 6c 6c 22 2c 22 68 5f 6f 73 22 3a 22 38 :"all","h_os":"8
0x1576d07a0: 2e 31 30 30 30 30 30 22 2c 22 61 75 74 6f 22 3a .100000","auto":
0x1576d07b0: 31 2c 22 68 5f 74 73 22 3a 31 35 33 39 37 34 37 1,"h_ts":1539747
0x1576d07c0: 30 39 35 37 31 32 2c 22 68 5f 6d 22 3a 34 38 38 095712,"h_m":488
0x1576d07d0: 33 36 37 38 36 2c 22 68 5f 69 64 66 61 22 3a 22 36786,"h_idfa":"
0x1576d07e0: 41 39 33 42 39 35 41 34 2d 39 30 43 33 2d 34 43 A93B95A4-90C3-4C
0x1576d07f0: 38 42 2d 39 38 41 38 2d 42 39 46 37 42 34 38 43 8B-98A8-B9F7B48C
0x1576d0800: 35 37 46 31 22 2c 22 68 5f 64 74 22 3a 31 7d 5a 57F1","h_dt":1}Z
0x1576d0810: 44 7b 22 64 69 72 65 63 74 69 6f D{"directio
经过观察发现进入函数时传的参数是post请求的参数内容 然后调用了string::append函数对传入的字符串追加了新的内容 "ZDY0MTBlODcx" 最后将字符串前十位和后十位进行交换得到我们上面所看到的文本
对“sub_100FB6090”代码还原实现如下:
std::string str = szData;
str.append("ZDY0MTBlODcx");
std::string strHead = str.substr(0, 10);
std::string strEnd = str.substr(str.length()-10, str.length());
str.replace(0, 10, strEnd);
str.replace(str.length()-10, str.length(), strHead);
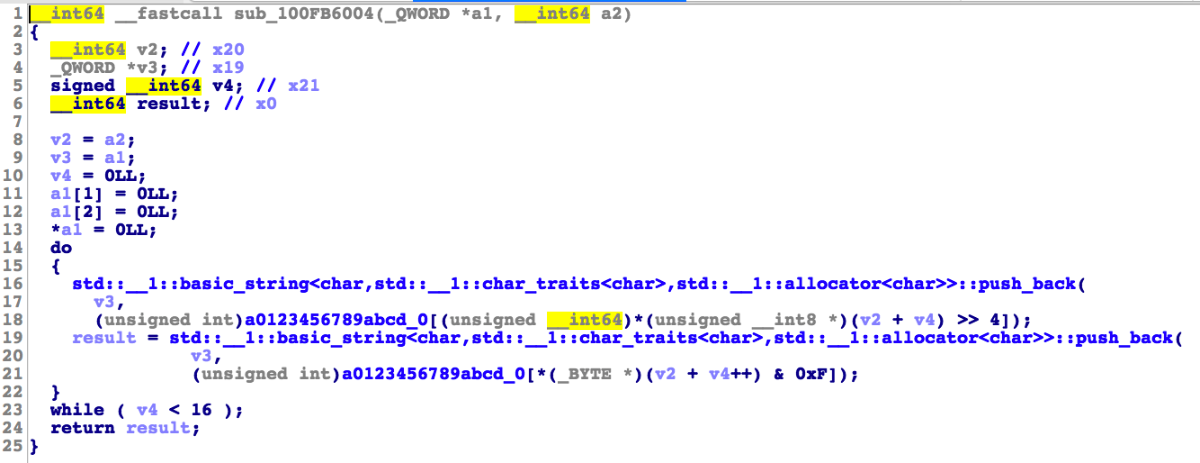
最后在调用“sub_100FB6004”时传入"sub_100DB274C"的返回值 最后返回了sign值 其中“sub_100FB6004”中有使用全局变量 直接使用x命令 复制出来即可
以下为还原后的c代码 可直接使用
// zuiyouEncryption.cpp :
//
#include "stdafx.h"
#include
#include
#include
#define u_int64_t unsigned long long
#define u_int32_t unsigned int
struct TAG_UINT64
{
u_int32_t low;
u_int32_t high;
void set(u_int32_t _high, u_int32_t _low){
this->high = _high;
this->low = _low;
}
};
u_int64_t qword_101126D90 = 0xEFCDAB8967452301;
u_int64_t qword_101126D98 = 0x1032547698BADCFE;
char a0123456789abcd_0[] = "0123456789abcdef";
unsigned char byte_101209EC8[] =
{
0x78, 0xA4, 0x6A, 0xD7, 0x56, 0xB7, 0xC7, 0xE8, 0xDB, 0x70, 0x20, 0x24, 0xEE, 0xCE, 0xBD, 0xC1, 0xAF, 0xF,
0x7C, 0xF5, 0x2A, 0xC6, 0x87, 0x47, 0x13, 0x46, 0x30, 0xA8, 1, 0x95, 0x46, 0xFD, 0xD8, 0x98, 0x80, 0x69, 0xAF, 0xF7, 0x44, 0x8B, 0xB1, 0x5B, 0xFF, 0xFF, 0xBE,
0xD7, 0x5C, 0x89, 0x22, 0x11, 0x90, 0x6B, 0x93, 0x71, 0x98, 0xFD, 0x8E, 0x43, 0x79, 0xA6, 0x21, 8, 0xB4, 0x49, 0x62, 0x25, 0x1E, 0xF6, 0x40, 0xB3, 0x40, 0xC0,
0x51, 0x5A, 0x5E, 0x26, 0xAA, 0xC7, 0xB6, 0xE9, 0x5D, 0x10, 0x2F, 0xD6, 0x53, 0x14, 0x44, 2, 0x81, 0xE6, 0xA1, 0xD8, 0xC8, 0xFB, 0xD3, 0xE7, 0xE6, 0xCD, 0xE1,
0x21, 0xD6, 7, 0x37, 0xC3, 0x87, 0xD, 0xD5, 0xF4, 0xED, 0x14, 0x5A, 0x45, 5, 0xE9, 0xE3, 0xA9, 0xF8, 0xA3, 0xEF, 0xFC, 0xD9, 2, 0x6F, 0x67, 0x8A, 0x4C, 0x2A,
0x8D, 0x42, 0x39, 0xFA, 0xFF, 0x81, 0xF6, 0x71, 0x87, 0x22, 0x61, 0x9D, 0x6D, 0xC, 0x38, 0xE5, 0xFD, 0x44, 0xEA, 0xBE, 0xA4, 0xA9, 0xCF, 0xDE, 0x4B, 0x60, 0x4B,
0xBB, 0xF6, 0x70, 0xBC, 0xBF, 0xBE, 0xC6, 0x7E, 0x9B, 0x28, 0xFA, 0x27, 0xA1, 0xEA, 0x85, 0x30, 0xEF, 0xD4, 5, 0x1D, 0x88, 4, 0x39, 0xD0, 0xD4, 0xD9, 0xE5, 0x99,
0xDB, 0xE6, 0xF8, 0x7C, 0xA2, 0x1F, 0x65, 0x56, 0xAC, 0xC4, 0x44, 0x22, 0x29, 0xF4, 0x97, 0xFF, 0x2A, 0x43, 0xA7, 0x23, 0x94, 0xAB, 0x39, 0xA0, 0x93, 0xFC, 0xC3,
0x59, 0x5B, 0x65, 0x92, 0xCC, 0xC, 0x8F, 0x7D, 0xF4, 0xEF, 0xFF, 0xD1, 0x5D, 0x84, 0x85, 0x4F, 0x7E, 0xA8, 0x6F, 0xE0, 0xE6, 0x2C, 0xFE, 0x14, 0x43, 1, 0xA3,
0xA1, 0x11, 8, 0x4E, 0x82, 0x7E, 0x53, 0xF7, 0x35, 0xF2, 0x3A, 0xBD, 0xBB, 0xD2, 0xD7, 0x2A, 0x91, 0xD3, 0x86, 0xEB, 0, 0, 0, 0, 0x80, 0x88, 0xE5, 0x40, 0,
0, 0, 0, 0, 0x7C, 0xD5, 0x40, 0x41, 0x42, 0x43, 0x44, 0x45, 0x46, 0x47, 0x48, 0x49, 0x4A, 0x4B, 0x4C, 0x4D, 0x4E, 0x4F, 0x50, 0x51, 0x52, 0x53, 0x54, 0x55, 0x56,
0x57, 0x58, 0x59, 0x5A, 0x61, 0x62, 0x63, 0x64, 0x65, 0x66, 0x67, 0x68, 0x69, 0x6A, 0x6B, 0x6C, 0x6D, 0x6E, 0x6F, 0x70, 0x71, 0x72, 0x73, 0x74, 0x75, 0x76, 0x77,
0x78, 0x79, 0x7A, 0x30, 0x31, 0x32, 0x33, 0x34, 0x35, 0x36, 0x37, 0x38, 0x39, 0x2B, 0x2F, 0xA2, 0xB4, 0xB7, 0x3E, 0x8F, 0x53, 0x34, 0x3F, 0x4D, 0x15, 0xC, 0x3E,
0, 0, 0, 0, 0x87, 0x16, 0x99, 0x3E, 0xA2, 0x45, 0x16, 0x3F, 0xD5, 0x78, 0xE9, 0x3D, 0, 0, 0, 0, 0xD8, 0xF0, 0x74, 0x3E, 0x69, 0x6F, 0xF0, 0x3E, 0, 0, 0, 0, 0,
0x80, 0x63, 0x40, 0x56, 0x56, 0x56, 0x56, 0x56, 0x56, 0xE6, 0x3F, 0, 0, 0, 0, 0, 0x60, 0x6C, 0xC0, 0x51, 0x46, 0x6F, 0xCB, 0x5A, 0x1D, 0x93, 0x3F, 0xD0, 0xB0,
0x2B, 0x40, 0xEE, 0x35, 0xD7, 0x3F, 0x39, 0xB4, 0xC8, 0x76, 0xBE, 0x9F, 0xCA, 0x3F, 0, 0, 0, 0, 0, 0xA0, 0x72, 0xC0, 0, 0, 0, 0, 0, 0xC0, 0x76, 0xC0, 0, 0,
0, 0, 0, 0xA0, 0x72, 0x40, 0, 0, 0, 0, 0, 0x40, 0x72, 0x40, 0, 0, 0, 0, 0, 0, 0x6F, 0x40, 0, 2, 0, 0, 0, 0x20, 0, 0, 0x46, 0x46, 0x49, 0x41, 0x66, 0x61, 0x34,
0x6D, 0x45, 0x56, 0x41, 0x57, 0, 0, 0, 0, 0, 0, 0, 0, 0xF3, 4, 0x35, 0xBF, 0, 0, 0, 0, 0x3A, 0xCD, 0x13, 0x3F, 0x3A, 0xCD, 0x13, 0xBF, 0, 0, 0, 0
};
u_int32_t _bic_(u_int32_t x,u_int32_t m) {
return x & (x ^ m);
}
u_int32_t _ror_(u_int32_t x, u_int32_t m) {
return (x >> m) | (x << (32 - m));
}
void sub_100DB274C(u_int64_t X0/*data*/, u_int64_t X1/*dataLen*/, u_int64_t X2/*outdata*/) {
u_int64_t X3 = 0;
u_int64_t X4 = 0;
u_int64_t X5 = 0;
u_int64_t X6 = 0;
u_int64_t X8 = 0;
u_int64_t X9 = 0;
u_int64_t X10 = 0;
u_int64_t X11 = 0;
u_int64_t i = 0;
u_int64_t X13 = 0;
u_int64_t X14 = 0;
u_int64_t X15 = 0;
u_int64_t X19 = 0;
u_int64_t X20 = 0;
u_int64_t X21 = 0;
u_int64_t X22 = 0;
u_int64_t X23 = 0;
u_int64_t X24 = 0;
u_int64_t X25 = 0;
u_int64_t X26 = 0;
u_int64_t X27 = 0;
char data[0x512] = {0};
u_int64_t var_120 = (u_int64_t)(data + 0x10);
u_int64_t var_118 = (u_int64_t)(data + 0x18);
u_int64_t var_108 = (u_int64_t)(data + 0x28);
u_int64_t var_100 = (u_int64_t)(data + 0x30);
u_int64_t var_FC = (u_int64_t)(data + 0x34);
u_int64_t var_F8 = (u_int64_t)(data + 0x38);
u_int64_t var_F4 = (u_int64_t)(data + 0x3C);
u_int64_t var_F0 = (u_int64_t)(data + 0x40);
u_int64_t var_E8 = (u_int64_t)(data + 0x48);
u_int64_t var_B0 = (u_int64_t)(data + 0x80);
u_int64_t var_AC = (u_int64_t)(data + 0x84);
u_int64_t var_A8 = (u_int64_t)(data + 0x88);
u_int64_t var_A0 = (u_int64_t)(data + 0x90);
u_int64_t var_98 = (u_int64_t)(data + 0x98);
*(u_int64_t*)var_120 = X2;
X2 = X1;
X3 = X0;
X6 = 0;
X20 = 0;
*(u_int64_t*)var_A8 = qword_101126D90;
*(u_int64_t*)var_100 = X2 << 3;
*(u_int64_t*)var_108 = X2 >> 0x1d;
X24 = var_E8;
X19 = X24 + 4;
*(u_int64_t*)var_A0 = qword_101126D98;
X21 = X24 + 0x38;
X5 = 0x67452301;
X23 = 0x10325476;
X22 = 0x98BADCFE;
X4 = 0xEFCDAB89;
X26 = (u_int64_t)&byte_101209EC8;
*(u_int64_t*)(var_118) = X19;
*(u_int64_t*)(var_118+0x8) = X21;
do
{
X8 = X2 - X20;
X27 = X8 > 0x3F ? 0x40 : X8;
X1 = X3 + X20;
if(X27 > 0x3F) {
X6 = 0;
}else {
((TAG_UINT64*)var_F8)->set((u_int32_t)X22, (u_int32_t)X23);
*(u_int64_t*)var_F0 = X20;
((TAG_UINT64*)var_FC)->low = (u_int32_t)X5;
X26 = X4;
X25 = X3;
X19 = X2;
X22 = var_98;
X2 = X27;
X0 = var_98;
X21 = X6;
X23 = X27;
memcpy((void*)X0, (void*)X1, X2);
X22 += X23;
X8 = 0x40 - X23;
X1 = X8;
X0 = X22;
memset((void*)X0, 0, (u_int32_t)X1);//BL _bzero
if(X21 == 0) {
((unsigned char*)X22)[0] = 0x80;
}
X1 = var_98;
X6 = 1;
X2 = X19;
X3 = X25;
X4 = X26;
X5 = (u_int32_t)*(u_int64_t*)var_FC;
X23 = *(u_int64_t*)var_FC >> 32;
X19 = *(u_int64_t*)var_118;
X21 = *(u_int64_t*)(var_118 + 0x8);
X20 = *(u_int64_t*)var_F0;
X22 = ((TAG_UINT64*)var_F4)->low;
X26 = (u_int64_t)&byte_101209EC8;
}
i = 0;
do{
((TAG_UINT64*)(X24 + i))->low = (u_int32_t)(((unsigned char*)(X1+1+i))[-1] | ((((unsigned char*)(X1+1+i))[0] | ((((unsigned char*)(X1+1+i))[1] | (((unsigned char*)(X1+1+i))[2] << 8)) << 8)) << 8));
}while((i += 4) != 0x40);
if(X27 <= 0x37) {
*(u_int64_t*)var_B0 = (u_int32_t)*(u_int64_t*)var_100;
*(u_int64_t*)var_AC = (u_int32_t)*(u_int64_t*)var_108;
}
i = 0;
X13 = X26 + 8;
X14 = X24 + 8;
X8 = X23;
X9 = X22;
X10 = X4;
X11 = X5;
do
{
X11 = _ror_((u_int32_t)((((_bic_((u_int32_t)X8, (u_int32_t)X10) | (X10 & X9)) + X11) + (u_int32_t)*(u_int64_t*)(X14-8)) + (u_int32_t)*(u_int64_t*)(X13-8)), 0x19) + X10;
X8 = _ror_((u_int32_t)((*(u_int64_t*)(X14 - 8) >> 32) + X8 + (*(u_int64_t*)(X13-8) >> 32) + ((X11 & X10) | _bic_((u_int32_t)X9, (u_int32_t)X11))), 0x14) + X11;
X9 = _ror_((u_int32_t)((u_int32_t)*(u_int64_t*)X14 + X9 + (u_int32_t)*(u_int64_t*)X13 + ((X8 & X11) | _bic_((u_int32_t)X10, (u_int32_t)X8))), 0xF) + X8;
X10 = _ror_((u_int32_t)((*(u_int64_t*)X14 >> 32) + X10 + (*(u_int64_t*)X13 >> 32) + ((X9 & X8) | _bic_((u_int32_t)X11, (u_int32_t)X9))), 0xA) + X9;
X14 += 0x10;
X13 += 0x10;
}while((i += 4) < 0x10);
i = 0;
X13 = X26 + 0x4C;
X14 = 0xA;
X15 = X19;
do
{
X11 = _ror_((u_int32_t)((((X10 & X8) | _bic_((u_int32_t)X9, (u_int32_t)X8)) + X11 + (u_int32_t)*(u_int64_t*)X15) + (u_int32_t)*(u_int64_t*)(X13-0xc)), 0x1B) + X10;
X8 = _ror_((u_int32_t)(X8 + ((u_int32_t)*(u_int64_t*)(X24 + (((X14 - 4) & 0xF) << 2))) + (*(u_int64_t*)(X13-0xc) >> 32) + ((X11 & X9) | _bic_((u_int32_t)X10, (u_int32_t)X9))), 0x17) + X11;
X9 = _ror_((u_int32_t)((u_int32_t)*(u_int64_t*)(X24 + (((X14 & 0xE) | 1) << 2)) + X9 + (u_int32_t)*(u_int64_t*)(X13-4) + ((X8 & X10) | _bic_((u_int32_t)X11, (u_int32_t)X10))), 0x12) + X8;
X10 = _ror_((u_int32_t)((u_int32_t)*(u_int64_t*)(X15-4) + X10 + (u_int32_t)*(u_int64_t*)X13 + ((X9 & X11) | _bic_((u_int32_t)X8, (u_int32_t)X11))), 0xC) + X9;
X13 += 0x10;
X15 += 0x10;
X14 += 0x14;
}while((i += 4) < 0x10);
i = 0;
X13 = X26 + 0x8C;
X14 = 5;
X15 = X21;
do
{
X11 = _ror_((u_int32_t)(((X9 ^ X8) ^ X10) + X11 + (u_int32_t)*(u_int64_t*)(X24 + ((X14 & 0xD) << 2)) + (u_int32_t)*(u_int64_t*)(X13-0xc)), 0x1C) + X10;
X8 = _ror_((u_int32_t)(X8 + (u_int32_t)*(u_int64_t*)(X24 + (((X14 + 3) & 0xF) << 2)) + (*(u_int64_t*)(X13-0xc) >> 32) + ((X11 ^ X10) ^ X9)), 0x15)+ X11;
X9 = _ror_((u_int32_t)(((u_int32_t)*(u_int64_t*)(X24 + (((X14 + 6) & 0xF) << 2))) + X9 + (u_int32_t)*(u_int64_t*)(X13-4) + (X8 ^ (X11 ^ X10))), 0x10) + X8;
X10 = _ror_((u_int32_t)((u_int32_t)*(u_int64_t*)X15 + X10 + (u_int32_t)*(u_int64_t*)X13 + ((X8 ^ X11) ^ X9)), 0x9) + X9;
X15 -= 0x10;
X13 += 0x10;
X14 += 0xC;
}while((i += 4) < 0x10);
i = 0;
X13 = X26 + 0xCC;
X14 = X21;
X15 = 0x15;
do
{
X11 = _ror_((u_int32_t)(((((X10 | (~X8)) ^ X9) + X11) + ((u_int32_t)*(u_int64_t*)(X24 + (((X15 - 0x15) & 0xC) << 2)))) + (u_int32_t)*(u_int64_t*)(X13-0xc)), 0x1A) + X10;
X8 = _ror_((u_int32_t)((u_int32_t)*(u_int64_t*)(X24 + (((X15 - 0xE) & 0xF) << 2)) + X8 + (*(u_int64_t*)(X13-0xc) >> 32) + ((X11 | (~X9)) ^ X10)), 0x16) + X11;
X9 = _ror_((u_int32_t)((u_int32_t)*(u_int64_t*)X14 + X9 + (u_int32_t)*(u_int64_t*)(X13-0x4) + ((X8 | (~X10)) ^ X11)), 0x11) + X8;
X10 = _ror_((u_int32_t)(((u_int32_t)*(u_int64_t*)(X24 + ((X15 & 0xF) << 2))) + X10 + (u_int32_t)*(u_int64_t*)X13 + ((X9 | (~X11)) ^ X8)), 0xB) + X9;
X13 += 0x10;
X14 -= 0x10;
X15 +=0x1C;
}while((i += 4) < 0x10);
X5 += X11;
X4 += X10;
X22 += X9;
X23 += X8;
((TAG_UINT64*)&X27)->high = 0;
X20 += X27;
}while(X27 >= 0x38);
i = 0;
((TAG_UINT64*)var_A8)->set((u_int32_t)X4, (u_int32_t)X5);
((TAG_UINT64*)var_A0)->set((u_int32_t)X23, (u_int32_t)X22);
X13 = *(u_int64_t*)var_120;
((unsigned char*)(X13))[0] = X5;
((unsigned char*)(X13))[1] = X5 >> 8;
((unsigned char*)(X13))[2] = X5 >> 0x10;
((unsigned char*)(X13))[3] = X5 >> 0x18;
((unsigned char*)(X13))[4] = X4;
((unsigned char*)(X13))[5] = X4 >> 8;
((unsigned char*)(X13))[6] = X4 >> 0x10;
((unsigned char*)(X13))[7] = X4 >> 0x18;
do
{
X10 = (u_int32_t)*(u_int64_t*)(((u_int64_t)var_A8 + 8) + i);
X11 = X13 + i;
((unsigned char*)(X11))[8] = X10;
((unsigned char*)(X11))[9] = X10 >> 8;
((unsigned char*)(X11))[0xA] = X10 >> 0x10;
((unsigned char*)(X11))[0xB] = X10 >> 0x18;
X10 = i + 0xC;
i = i + 4;
}while(X10 < 0x10);
}
void sub_100FB6004(u_int64_t outData, u_int64_t inData) {
u_int64_t i = 0;
do{
((unsigned char*)(outData))[i*2] = a0123456789abcd_0[(((unsigned char*)(inData))[i]) >> 4];
((unsigned char*)(outData))[i*2+1] = a0123456789abcd_0[(((unsigned char*)(inData))[i]) & 0xF];
}while((i += 1) < 0x10);
}
std::string calcSign(const char* szData) {
std::string str = szData;
str.append("ZDY0MTBlODcx");
std::string strHead = str.substr(0, 10);
std::string strEnd = str.substr(str.length()-10, str.length());
str.replace(0, 10, strEnd);
str.replace(str.length()-10, str.length(), strHead);
char szBuff[64] = {0};
char szSign[64] = {0};
std::string strRet = "";
sub_100DB274C((u_int64_t)str.c_str(), str.length(), (u_int64_t)szBuff);
sub_100FB6004((u_int64_t)szSign, (u_int64_t)szBuff);
strRet = szSign;
return strRet;
}
int main(int argc, char* argv[])
{
std::string sign = "";
const char* data = "{\"h_model\":\"iPhone 7\",\"h_ch\":\"appstore\",\"phone\":\"15658195157\",\"no_hash_code\":1,\"region_code\":86,\"h_app\":\"zuiyou\",\"type\":\"reg\",\"h_ts\":1539152851066,\"h_av\":\"4.6.4\",\"h_nt\":1,\"h_did\":\"32086bc6014d1a8a447100a065a21edc\",\"h_m\":95849495,\"h_os\":1030000,\"token\":\"T4K2Nn_Be6gYozzVxZd0Liea7qDY1cn75TJlGmRz6cH7kwagjSU5JrAW2CmeBiPozxpOf\",\"h_dt\":1}";
DWORD dwStartTime = GetTickCount();
sign = calcSign(data);
printf("sign: %s\r\n", sign.c_str());
return 0;
}
以上就是对sign值生成过程的全部分析记录 至于POST数据字段都是怎么来的可以按照上述步骤查找到




 微信收款码
微信收款码 支付宝收款码
支付宝收款码